The Invisible Cut: Why Post-Production Must Take Data Security Seriously
In post, we obsess over what the audience sees.
Noise floors. Colour trims. Subtitle alignment. Delivery specs down to the codec profile.
But the real risk in post-production isn’t creative.
It’s structural.
And in 2026, security is no longer an IT discussion — it’s a business one.
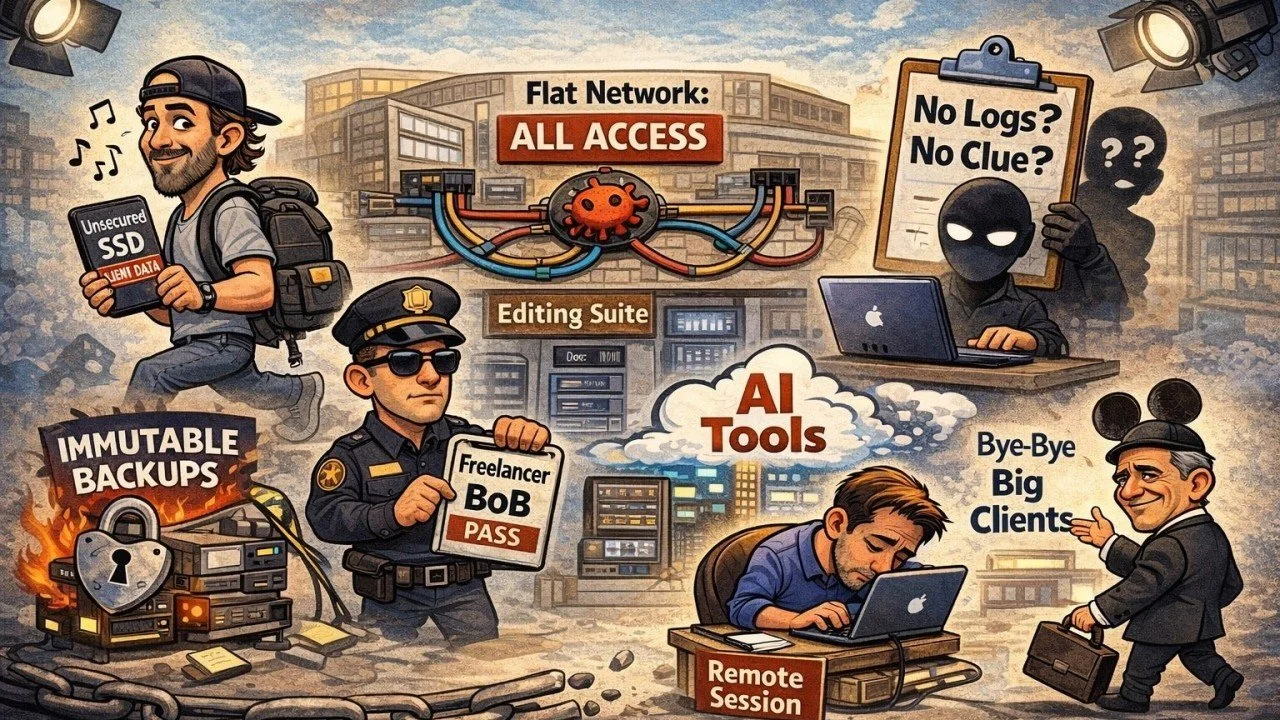
The Portable Drive Problem (One Small Example)
Let’s address one obvious issue...briefly.
Freelancers carrying client assets on unsecured SSDs.
It happens daily.
Unencrypted drives. Multiple system connections. No logging. No audit trail.
If that drive is lost, cloned, or infected, you don’t just lose data.
You inherit liability.
But portable media is just one symptom.
The real issue is architectural.
Security Is a System — Not a Policy
Frameworks like the Trusted Partner Network (TPN) exist for a reason.
Not to tick boxes.
To force post facilities to think in layers.
Here are five areas where serious facilities separate themselves from hopeful ones:
Network Segmentation
Flat networks are dangerous.
Editors, assistants, render nodes, admin machines — all on the same subnet?
One compromised device shouldn’t expose the entire SAN.
Segmentation ensures:
Project isolation
Role-based access
Contained breaches
Controlled remote entry points
Without segmentation, you don’t have defense. You have optimism.
Access Control & Least Privilege
Not everyone needs access to everything.
TPN-aligned environments enforce:
Role-based permissions
Time-bound access
Project-specific credentials
Revocation protocols
Freelancer finishes a job?
Access ends.
No lingering permissions. No dormant accounts.
Because dormant accounts become entry points.
Logging & Audit Trails
If you can’t see it, you can’t secure it.
Serious post facilities maintain:
Login tracking
File access logs
Admin change records
Remote session auditing
When a platform like Netflix or Amazon Studios evaluates a vendor, they’re not asking if you “feel secure.”
They’re asking:
Can you prove it?
Secure Remote Workflows
Remote editing isn’t going away.
But shipping drives is not a strategy.
Secure remote architecture should include:
Controlled gateway access
Encrypted connections
No local media caching
Monitored session logging
Storage that remains centralized
The goal isn’t restricting creativity.
It’s removing uncontrolled data movement.
Immutable Backups & Disaster Recovery
Ransomware doesn’t care about your delivery schedule.
Without:
Immutable snapshots
Offsite redundancy
Documented restore procedures
Regular recovery testing
…your backup strategy is theoretical.
And theory doesn’t restore corrupted masters.
Security Is Now a Revenue Filter
High-value clients don’t just assess your reel.
They assess your risk.
Studios and streamers — including The Walt Disney Company — operate under governance models that demand structured vendor security.
If your infrastructure isn’t documented, segmented, monitored, and auditable, you limit the tier of projects you can attract.
Security maturity determines market access.
The Industry Has Changed
Post-production is now:
Cloud-connected
AI-assisted
Globally distributed
Data-intensive
Every integration increases exposure.
The old model of:
“We trust our team.”
Is no longer sufficient.
Trust without architecture is risk.
The Hard Truth
No one believes they need serious security.
Until they do.
In post-production, we don’t just move files.
We handle unreleased intellectual property worth millions.
The most dangerous threat isn’t a hacker in a hoodie.
It’s complacency.
In 2026 and beyond, the cleanest cut isn’t the one the audience sees.
It’s the one where risk never reaches the timeline.
And that cut starts with taking data security seriously.